Burp Suite Free Edition 1.5 Download
Feb 25, 2018 - Burp Suite Professional version 1.5.01 Free Download at Nz Paper. Burp Suite Free Edition 1.5 Download. Today, this post is intended to. Amsco examiner 10 service manual.
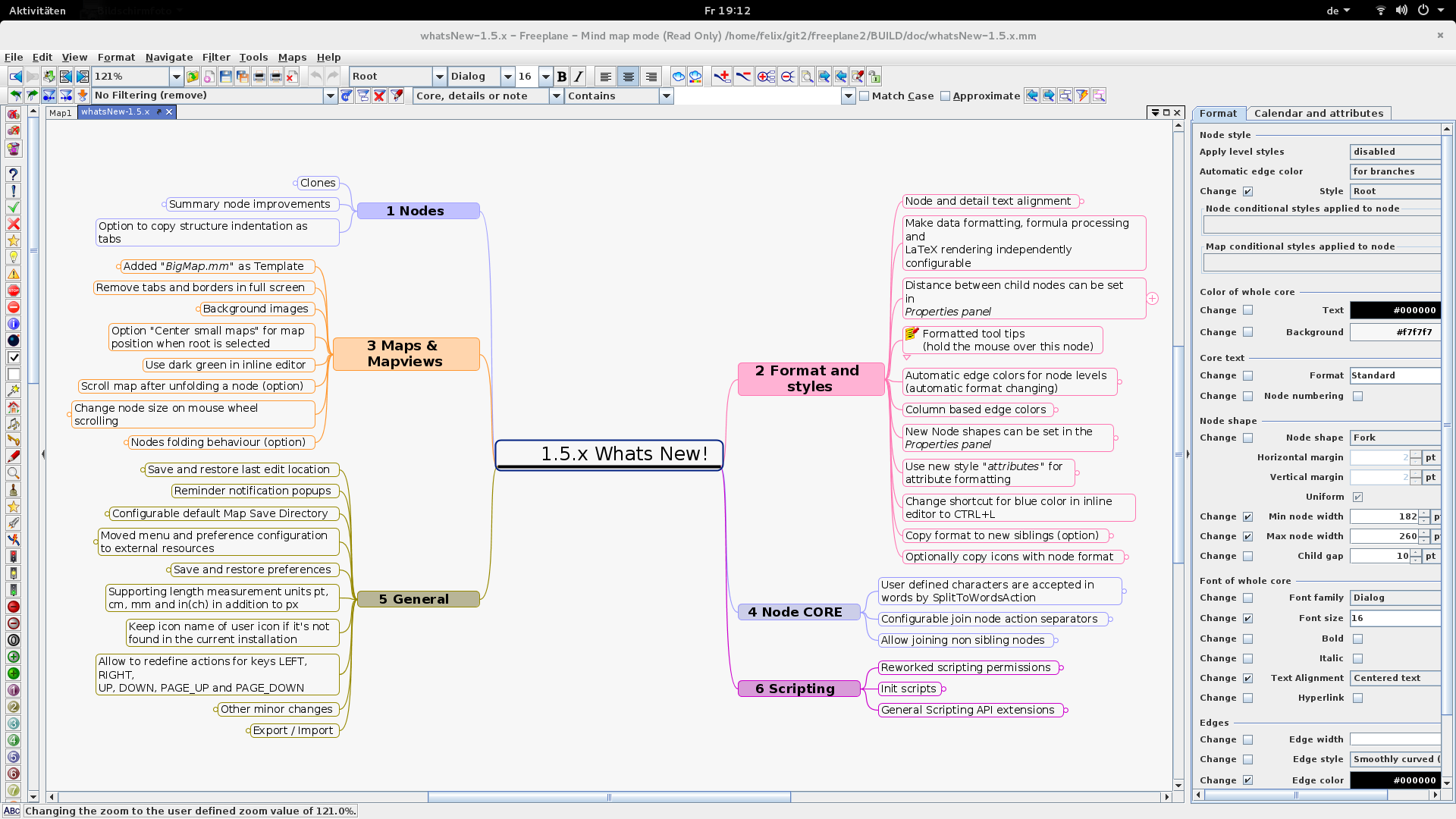
Download Crack Burp Suite crack Activated With Serial Key Full Version Burp Suite 1.7 Keygen Crack is the world best security application which keep you in eyes view your network traffic through browser. Burp suite 1.7 pro crack will capture all the HTTP and HTTPS traffic going through your browser so that you can test the security of the web applications currently open in the browser. Burp suite 1.7 crack is an integrated platform for performing security testing of web applications. The Burp suite 1.7.35 Patch user interface provides quick access to numerous testing tools: Target, Proxy, Spider, Scanner, Intruder, Repeater, Sequencer, Decoder, Comparer, and Extender. You can send messages between these tools with Burp suite crack linux and create numerous scenarios in order to detect possible vulnerabilities.
Burp suite Full Version supports Mac OS X (Universal Binary) only. Mirror Download Link Burp suite unlimited various tools work seamlessly together to support the entire testing process, from initial mapping and analysis of an application’s attack surface, through to finding and exploiting security vulnerabilities. Burp suite apk provides quick access to a collection of testing tools that can help you identify possible vulnerabilities as far as your web applications are concerned. The Burp suite professional downloadruns on the Java platform and delivers full control over the included security testing tools. Burp suite pro github gives you full control, letting you combine advanced manual techniques with state-of-the-art automation, to make your work faster, more effective, and more fun.
Burp Suite 1.7.35 Keygen Features: • An Intruder tool, for performing powerful customized attacks to find and exploit unusual vulnerabilities. • Ability to “passively” spider an application in a non-intrusive manner, with all requests originating from the user’s browser. • functionality of Burp Suite.
Data processed by one tool can be used in arbitrary ways to affect the behaviour and results of other tools. • One-click transfer of interesting requests between tools, e.g. From the Burp Proxy request history, or the Burp Spider results tree. • Extensibility via the IBurpExtender interface, which allows third-party code to extend the • Centrally configured settings for downstream proxies, web and proxy authentication, and logging. • Extensibility, allowing you to easily write your own plugins, to perform complex and highly customized tasks within Burp. • Tools can run in a single tabbed window, or be detached in individual windows. • All tool and suite configuration is optionally persistent across program loads.
Fonts similar to 'Prov Architect NDP': 1 of 30. Prov Architect NDP: P22 FLLW Exhibition: Architectural Lettering. Prov architect ndp font. Designed after the unique handwriting style of Architects. This typeface reflects a more quickly jotted notation style than its sister font, Prov Draftsman NDP. Instead of lowercase characters it contains smaller caps like actual hand drawn blueprints etc. Also note the ` key has been changed to the. Prov Architect NDP - Webfont & Desktop font « MyFonts. Designed after the unique handwriting style of Architects. This typeface reflects a more quickly jotted notation style than its sister font, Prov Draftsman NDP. Information about the font Prov Architect NDP and where to buy it. Prov Architect NDP Desktop EULA Webfont: for your website A webfont license allows you to embed the font into your website, so that it can be displayed on any browser.
• Detailed analysis and rendering of requests and responses. • An intercepting Proxy, which lets you inspect and modify traffic between your browser and the target application. • An application-aware Spider, for crawling content and functionality. • An advanced web application Scanner, for automating the detection of numerous types of vulnerability.
• Detailed analysis and rendering of requests and responses. • A Repeater tool, for manipulating and resending individual requests.